21 CFR Part 11
DataNinja automation technology addresses 21 CFR Part 11 requirements.
What you need to know about FDA regulations for electronic records:
The 21 CFR Part 11 rule on electronic records and electronic signatures became effective in August of 1997. Since then, there has been an ongoing discussion in the regulated industry and its suppliers about the correct interpretation and implementation of the resulting requirements. While the general implications are clear today, there is still some need for clarification of the detailed implementation. The FDA supports this process by providing a set of forthcoming guidance documents, e.g. on terminology, validation, audit trail, and archiving issues.
Strongly committed to GxP compliance of its products and services, DataNinja keeps track of any evolving new requirements and interpretations. New insights are fed back to product development in an immediate and continuous manner.
The purpose of this document is to demonstrate the compliance of DataNinja's MES Inventory and Manufacturing Suite solutions with 21 CFR Part 11 as far as technical and functional requirements are affected.
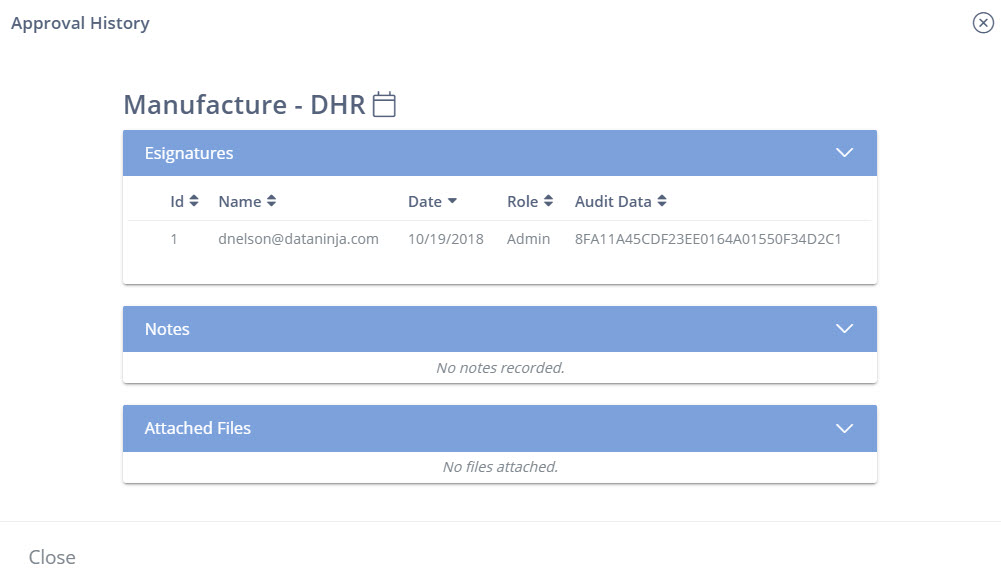
21 CFR part 11 Electronic Signature Approval History Audit Trail.
Validation
Validation is mandatory for every system related to 21 CFR Part 11. The validation has to be accomplished during system integration. DataNinja offers a comprehensive computer system validation consultancy that comprises of the appropriate validation documentation templates and active support in every step of a validation project.
DataNinja Inventory and Manufacturing is prepared to be validated. It has successfully passed all qualification steps for 21 CFR Part 11 that can be performed independently from its final application. Final validation in the production environment may include additional configuration and extension as well as installation, operational, and performance verification. If needed, hardware installation verification should include devices like scales and printers, scanners.
21 CFR Part 11 Requirement Trace Matrix
This initial checklist for closed system introduces our system support.
Section | 21 CFR Part 11 Regulation Text | DataNinja Implementation and Application |
|---|---|---|
B-11.10 | Persons who use closed systems to create, modify, maintain, or transmit electronic records shall employ procedures and controls designed to ensure the authenticity, integrity, and, when appropriate, the confidentiality of electronic records, and to ensure that the signer cannot readily repudiate the signed record as not genuine. Such procedures and controls shall include the following: | The end-user and manufacturer are responsible for developing procedures to support automation applications in regulated environments. |
(a) | Validation of systems to ensure accuracy, reliability, consistent intended performance, and the ability to discern invalid or altered records. | Our customers need to validate their installation. We help |
(b) | The ability to generate accurate and complete copies of | Configuration as well as production data, like recorded history, audit trails or batch reports, can be exported or archived. The information is available online to the authorized operator in either standard or customized displays, or can be printed or exported. |
(c) | Protection of records to enable their accurate and ready retrieval throughout the records retention period. | Our experts help our customers fulfill business and regulatory drivers associated with record retention by defining appropriate procedures for access, archival and retrieval of records. |
(d) | Limiting system access to authorized individuals. | Standard procedures to limit physical access are the |
(e) | Use of secure, computer-generated, time-stamped audit trails to independently record the date and time of operator entries and actions that create, modify, or delete electronic records. Record changes shall not obscure previously recorded information. Such audit trail documentation shall be retained for a period at least as long as that required for the subject electronic records and shall be available for agency review and copying. | The audit trail is an integrated system function. In general, historical data cannot be altered. |
(f) | Use of operational system checks to enforce permitted sequencing of steps and events, as appropriate. | DataNinja sequencing supported in Labor Steps, Trackable Attributes, Inspection Attributes and https://docs.dataninja.com/docs/required-parts. See Part and BOM configuration. |
(g) | Use of authority checks to ensure that only authorized | The system restricts access according to the user and user role configuration. The rules relate to the use of system functions. |
(h) | Use of device (e.g., terminal) checks to determine, as appropriate, the validity of the source of data input or operational instruction. | The functional scope of devices (Tablets, Mobile Devices, Desktop/Laptop Computers) is determined during system configuration. DataNinja is browser based. |
(i) | Determination that persons who develop, maintain, or use electronic record/electronic signature systems have the education, training, and experience to perform their assigned tasks. | The customer is responsible for ensuring that personnel |
(j) | The establishment of, and adherence to, written policies that hold individuals accountable and responsible for actions initiated under their electronic signatures, in order to deter record and signature falsification. | The system owner is responsible for defining the policy for the manufacturing or production facility. |
(k) | Use of appropriate controls over systems documentation including: | The customer’s organization is responsible for ensuring change control procedures for operational and maintenance documentation. DataNinja consultants are prepared to help customers. |
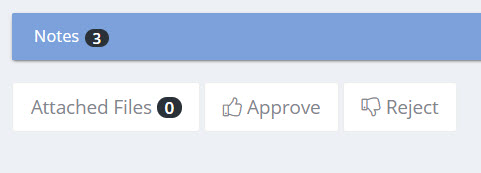
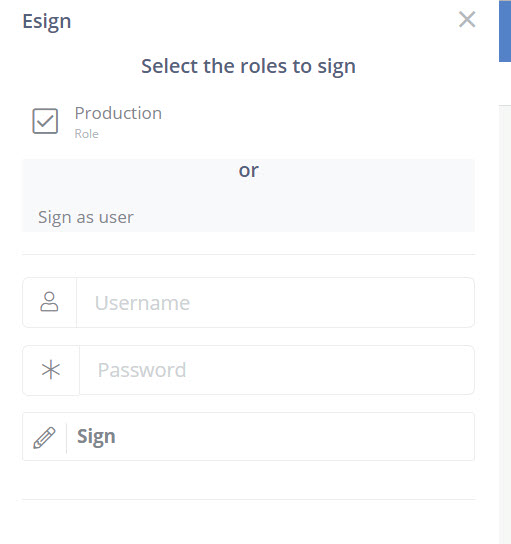
B-11.50 (a) | Signed electronic records shall contain information associated with the signing that clearly indicates all of the following: | When electronic records are signed, the system records the following items as part of the electronic signing process: |
(b) | The items identified in paragraphs (a)(1), (a)(2), and (a)(3) of this section shall be subject to the same controls as for electronic records and shall be included as part of any human readable form of the electronic record (such as electronic display or printout). | The electronic record includes the signature aspect, which is stored in the same system database. The system allows the display the electronic signature as described in 11-50 (a) either on the screen(MD5) or in a report. |
B-11.70 | Electronic signatures and handwritten signatures executed to electronic records shall be linked to their respective electronic records to ensure that the signatures cannot be excised, cop-ied, or otherwise transferred to falsify an electronic record by ordinary means. | The signature event, with an explanation of the status or reason (such as “approved” or “maintenance action”), is linked to the electronic record and securely archived with the record and through the audit trail. |
C-11.100 (a) | Each electronic signature shall be unique to one individual and shall not be reused by, or reassigned to, anyone else. | All user identification and password combinations are unique. |
(b) | Before an organization establishes, assigns, certifies, or otherwise sanctions an individual’s electronic signature, or any element of such electronic signature, the organization shall verify the identity of the individual. | The customer organization is responsible for assigning access rights to operators and other users, which allow them to use our system. |
(c) | Persons using electronic signatures shall, prior to or at the time of such use, certify to the agency that the electronic signatures in their system, used on or after August 20, 1997, are intended to be the legally binding equivalent of traditional handwritten signatures. | Our customers are responsible for submitting a certification to the agency that the electronic signatures used in their system are intended to be the legally binding equivalent of traditional handwritten signatures. |
C-11.200 (a) | Electronic signatures that are not based upon biometrics shall:(1) Employ at least two distinct identification components such as an identification code and password. | For security, our system requires two components for authorization and electronic signatures, the user identification and password. The system distinguishes between an electronic signature assigned and linked to an electronic record, and an authorization for controlled system access The user must enter his or her user ID and password for each separate signature action. |
C-11.200 (a) | (ii) When an individual executes one or more signings not performed during a single, continuous period of controlled system access, each signing shall be executed using all of the electronic signature components. | Each signer must identify him or herself with unique user ID and password, irrespective of the type of signature requested: 1st or 2nd signatures from an individual or a member of a user group. Our customers need to set up appropriate procedures and policies. |
(b) | Electronic signatures based upon biometrics shall be designed to ensure that they cannot be used by anyone other than their genuine owners. | |
C-11.300 (a) | Persons who use electronic signatures based upon use of identification codes in combination with passwords shall employ controls to ensure their security and integrity. Such controls shall include: | Every combination of user identification and password is unique. |
(b) | Ensuring that identification code and password issuances are periodically checked, recalled, or revised (e.g., to cover such events as password ageing). | In addition to organizational procedures, the system technology supports password ageing and minimum password length and prevents the reuse of a configurable number of prior pass-words. |
(c) | Following loss management procedures to electronically deauthorize lost, stolen, missing, or otherwise potentially compromised tokens, cards, and other devices that bear or generate identification code or password information, and to issue temporary or permanent replacements using suitable, rigorous controls. | Our customer is responsible for defining procedures for handling forgotten or lost passwords. If you need help in this process, please contact DataNinja Support |
(d) | Use of transaction safeguards to prevent unauthorized use of passwords and/or identification codes, and to detect and report in an immediate and urgent manner any attempts at their unauthorized use to the system security unit, and, as appropriate, to organizational management. | Built in security which allows the system to disable a user’s account after consecutive failed logins. Failed attempts to login, authorize or electronically sign records are logged as audit trail events by the system. |
(e) | Initial and periodic testing of devices, such as tokens or cards, that bear or generate identification code or password information to ensure that they function properly and have not been altered in an unauthorized manner. | This is the responsibility of the system owner. Our experts can support this effort. |
Updated 6 months ago
